AFG Intel Wire - The Pattern Buried Inside Epsteins Flight Log
A Deep-Dive Assessment of Intent, Risk Management, and What the Recordkeeping
The Pattern Buried Inside Epstein’s Handwritten Flight Logs
A Deep-Dive Assessment of Intent, Risk Management, and What the Recordkeeping Really Suggests
By: Timothy Times
November 16, 2025
(Based on flightlog contained within the Full Jeffrey Epstein File Release. To read that article and download the complete file release click below)
The handwritten flight logs tied to Jeffrey Epstein’s aircraft have long been treated as mundane aviation paperwork, a rough administrative ledger, a pilot’s personal notes, a static piece of evidence. When these logs are examined not as travel records but as operational artifacts, an entirely different picture emerges. The details are not random. The inconsistencies are not sloppy. The omissions are not accidental.
Across the pages, a pattern takes shape. The logs separate insiders from outsiders, shield certain individuals while exposing others, and document human beings with coded shorthand that aligns more closely with covert transport and trafficking concealment than with any legitimate aviation practice.
This is not the record of a careless pilot. It is the blueprint of a controlled environment.
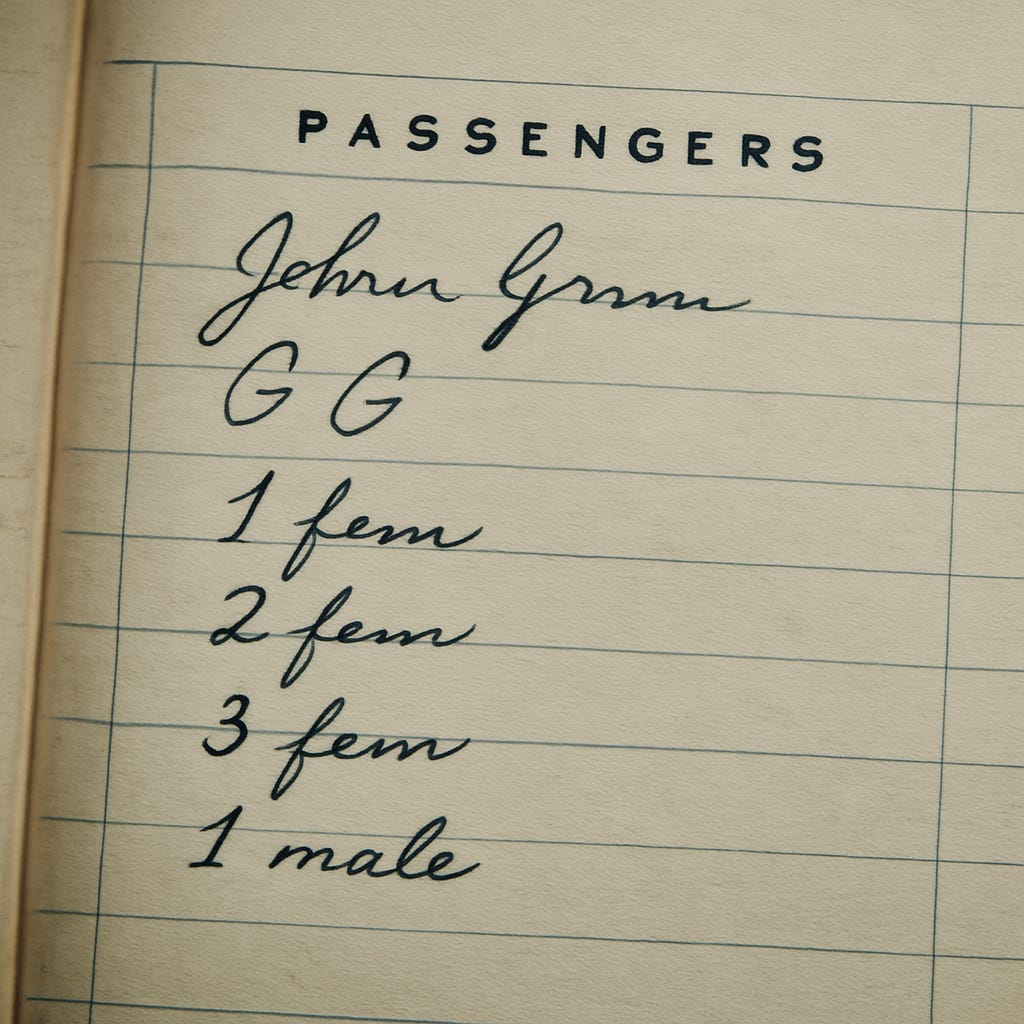
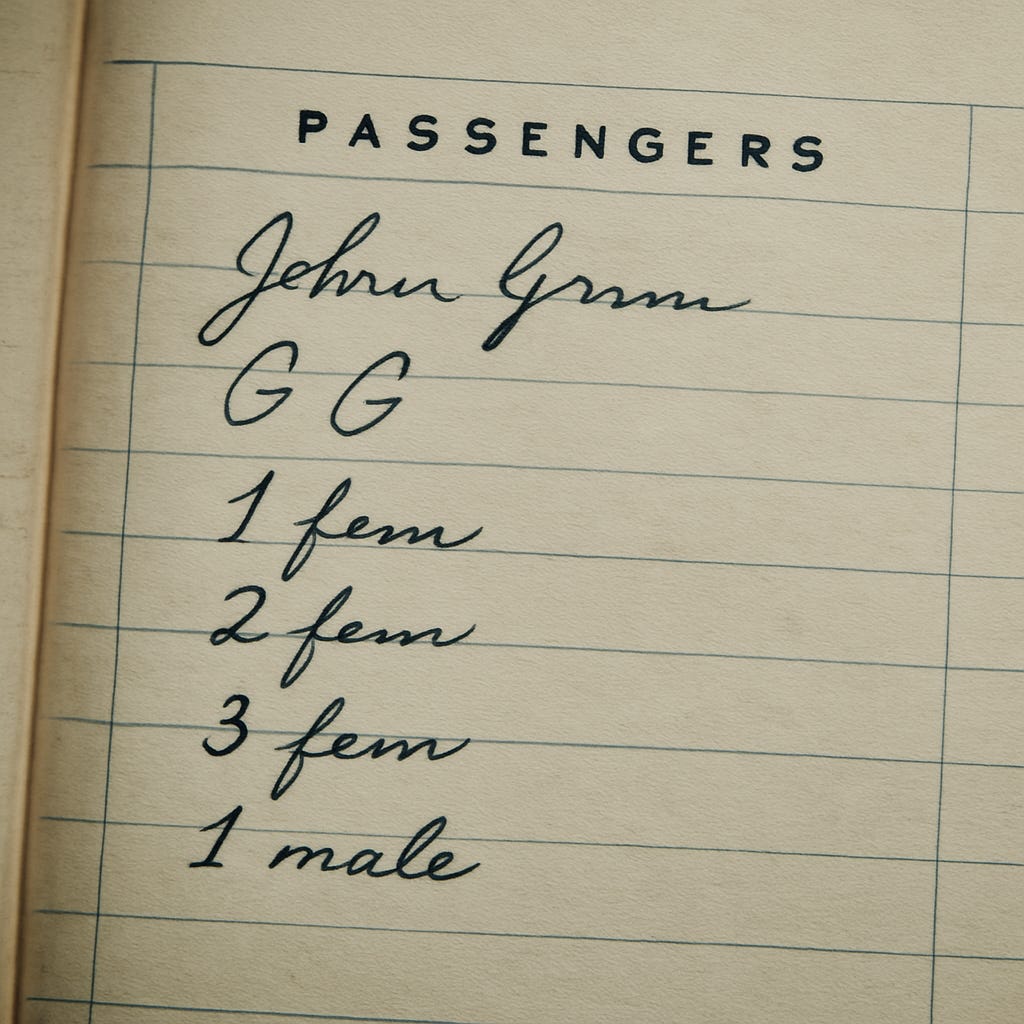
The handwriting is degraded. The OCR is unreliable. But the structural behavior is unmistakable. Early pages list full names. Later pages shift abruptly into initials. Anonymous passengers are logged only as “1 fem” or “2 male.” VIPs are still recorded in full while insiders vanish behind initials and minors or vulnerable individuals disappear behind numbers. This is a dual-purpose documentation system that obscures criminal activity while preserving leverage over powerful visitors.
Below is a full analytical assessment of how that pattern operates, what it implies, and why it matters.
Structured Analytical Assessment
The Passenger Recording Pattern in Epstein’s Flight Logs
Executive Summary
A close review of the handwritten pilot logbooks attributed to Epstein’s aircraft reveals a deliberate and systematic shift in how passengers were recorded over time. The pattern strongly suggests a dual-track documentation strategy. One track focuses on concealment for insiders and co-conspirators. The other track focuses on exposure for outside VIPs. This structure supports both operational deniability and blackmail viability, two characteristics commonly observed in trafficking networks and power leverage ecosystems.
1. Foundational Pattern: The Switch From Names to Initials
Early in the logbook sequence, the pilot records full and unambiguous names for:
Jeffrey Epstein
Ghislaine Maxwell
Members of the regular aircraft crew
Select recurring adult passengers
This aligns with normal aviation recordkeeping.
Later, the pattern changes abruptly:
Epstein becomes “JE”
Maxwell becomes “GM”
Core associates appear only as initials
This is not a necessary operational change. It is a tactical decision that reduces identifiability for the individuals most central to the enterprise. It establishes a layer of deniability.
2. Introduction of “1 fem / 2 male / 3 fem” Notation
At the same time, the pilot begins recording additional passengers as:
“1 fem”
“2 fem”
“3 fem”
“1 male”
This shorthand violates standard aviation norms.
Minors must be named in compliant flight records.
Adults are typically listed for liability and insurance requirements.
The quantity-and-gender notation aligns with:
Concealing trafficked individuals
Masking minors
Obscuring identity and age
Avoiding traceability
This is one of the clearest indicators of trafficking concealment behavior in the logs.
3. The Most Telling Element: VIPs Are Still Written Out in Full
While Epstein, Maxwell, and internal personnel are reduced to initials, prominent outside passengers continue to be recorded with full names. These include:
Political figures
Business leaders
Academics
Celebrities
Philanthropists
The pattern is consistent:
VIPs are always named in full
Vulnerable or illicit passengers are recorded vaguely
Epstein’s inner circle is protected by initials
This asymmetric structure resembles a deliberate evidentiary trap. It protects insiders while preserving leverage over outsiders.
When a VIP is on board:
Epstein is initialed
Maxwell is initialed
Additional females are listed numerically
The VIP is fully named
The outsider becomes clearly documented. The insider becomes obscured. The vulnerable passengers become invisible.
4. Operational Interpretation: A Dual-Purpose Documentation System
Epstein’s logbook behavior aligns with two strategic objectives.
A. Deniability for the Inner Network
Initials create plausible distance. This allows the claim that the initials do not necessarily refer to Epstein or Maxwell. The logs are built to obscure internal accountability.
B. Exposure for High-Value Outsiders
VIPs receive full-name entries with no ambiguity. When these names appear beside vague notations like “2 fem,” the structure creates implied proximity without naming the vulnerable individuals.
This mirrors the way kompromat frameworks operate:
Outsiders become highly identifiable
Insiders remain semi-anonymized
Illicit passengers are untraceable
This is the architecture of a controlled environment where access creates vulnerability.
5. Escalation Profile Over Time
The behavior in the logs evolves across three clear phases.
Early Phase
Clean recordkeeping
Full names
Standard practice
Mid Phase
Introduction of gender-count notations
First appearance of initials
Rising number of unnamed passengers
Late Phase
Epstein, Maxwell, and staff appear only as initials
Nearly every additional passenger appears as “1 fem,” “2 fem,” and similar labels
VIP names remain spelled out
Unnamed female passenger counts increase significantly
This is the behavioral signature of an operation that becomes:
More concealed
More confident
More systematic
More compartmentalized
More focused on leverage and secrecy
6. Compliance, Visibility, and Blackmail Dynamics
The structure of the logs supports a three-layer control model.
1. Internal Protection
Initials and numeric descriptors prevent investigators from reconstructing identities or connections.
2. External Exposure
Full VIP names anchor powerful individuals to specific flights and dates.
3. Narrative Control
Selective clarity allows Epstein’s operation to deny, weaponize, or reinterpret entries.
This architecture is consistent with trafficking networks that intersect with political, financial, and social power structures.
7. Conclusion
The handwritten flight logs do not behave like standard pilot notes. They behave like intentionally structured documents built to conceal illicit activity and leverage influential individuals.
Epstein’s circle is anonymized
Vulnerable passengers are reduced to numbers
Prominent visitors are recorded permanently and unambiguously
This pattern is not incidental. It is engineered, repeatable, and strategic.
These logs were not designed merely to record flights. They were designed to manage risk, preserve deniability, and maintain leverage. These are foundational components of a trafficking ecosystem and a blackmail network operating in parallel.



🚩The "upper class" protects PEDOPHILES‼️
None of them give a shit that they and their PEDOPHILE bffs, would hurt, torture, rape, and sexual assault CHILDREN!! These FUCKKKS actually enjoy hurting children. I wonder if thats why they tried to ban abortions Nation wide😑
🚩Also, is this why the GOP keeps lowering the legal age of marriage for little girls.
All of their names should be brought to light🤬💯
ALSO, MEGYN KELLY CAN GO TO HELL!
She said that a 15 year old is NOT a child!
Stupid ass, cunt!
✨️🤍 I WILL FOREVER STAND WITH THE VICTIMS 🤍
✅️Thank you for all of this new data, AFG TEAM✨️
makes perfect sense....name the big guns for your protection and to keep them beholden. Itemize the 'product', because, to them, that's all these girls were. :(